According to assessments by the United Nations, North Korea has emerged as the leading government-backed source of cryptocurrency theft worldwide. Much of this activity has been attributed to state-linked hacking units, most notably the Lazarus Group, which Western governments and the UN Panel of Experts identify as operating under the direction of Pyongyang’s intelligence services. UN reporting estimates that North Korean–associated groups have stolen billions of dollars in digital assets over recent years, turning crypto into a significant external revenue stream for a regime operating under extensive international sanctions.
In 2025, the Multilateral Sanctions Monitoring Team reported that North Korean cyber operations stole at least $1.65bn in digital assets between January and September alone, including approximately $1.4bn from a single breach at the crypto exchange Bybit in February. This followed an estimated $1.2bn in cryptocurrency theft during 2024.
The monitoring team concluded that these proceeds are being channelled into weapons of mass destruction and ballistic missile programmes, directly linking crypto crime to prohibited state activity.
These attacks follow a clear pattern. Instead of exploiting complex flaws in blockchain software, North Korean hackers increasingly target large, centralised crypto exchanges and custodial platforms. These companies, such as Bybit, Atomic Wallet and Coinspaid, hold vast amounts of customer funds in one place, making them attractive targets.
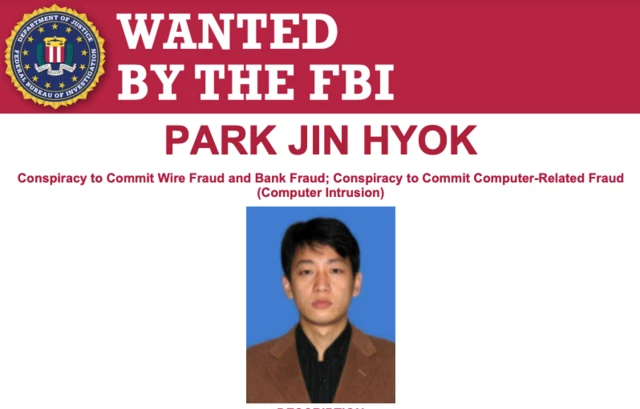
In many cases, the breach does not begin with advanced code but with people. UN and US authorities have warned that attackers often gain access by tricking employees through fake job offers or infected files that appear routine. Once inside internal systems, hackers can move funds at scale, often without triggering immediate alarms. Experts report that these hackers are often working nearly 24 hours a day.
Once assets are taken, laundering rarely relies on a single tool. Blockchain tracing firms such as Chainalysis and TRM Labs report that stolen assets are moved across different networks and intermediaries before reaching over-the-counter brokers and informal financial channels, largely in East and Southeast Asia. This process slows enforcement and complicates attribution, even though the transactions themselves remain visible on public ledgers.
Western governments have responded with sanctions for financial institutions. Yet UN reporting continues to show that uneven enforcement across countries limits the practical impact of sanctions. Differences in legal authority and regulatory capacity allow stolen funds to move through jurisdictions with weaker oversight, often faster than authorities can coordinate responses or freeze assets.
As crypto markets integrate further into global finance, the challenge is no longer whether illicit flows can be identified, but whether intervention can occur fast enough to prevent conversion into usable capital.
North Korea’s use of cryptocurrency illustrates how quickly financial technology can acquire geopolitical consequences. Digital assets have increased efficiency and cross-border access, but they have also exposed weaknesses in enforcement frameworks designed for conventional banking.
Has crypto revealed the limits of sanctions designed for a world of banks, not blockchains?
North Korea’s experience suggests that it has.
Modern sanctions regimes rely on control over regulated financial intermediaries. Banks and payment networks create chokepoints where states can freeze assets and deny access. This model assumes that large financial flows pass through institutions subject to national regulation and enforcement.
Cryptocurrency weakens these assumptions. While blockchains are transparent, enforcement still depends on legal authority at the points where digital assets are converted into usable capital. Those points are unevenly regulated across jurisdictions.
This mismatch has allowed North Korea to adapt faster than the sanctions designed to constrain it. UN reporting links major crypto thefts to the Lazarus Group. As sanctions restricted North Korea’s access to the formal banking system, cryptocurrency provided an alternative means of moving and storing value outside regulated financial channels, particularly before funds reached points where legal oversight applied.
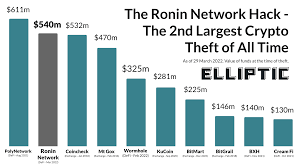
Lazarus’ operations also challenge common assumptions about cybercrime. These attacks are not financially opportunistic. They are carefully targeted and aligned with state priorities. One of the clearest examples is the 2022 hack of the Ronin Network, which US authorities and the UN Panel of Experts attributed to Lazarus and valued at more than $600mn. UN investigators have stated that proceeds from such operations are used to support prohibited weapons programmes, placing these hacks within the realm of national security rather than conventional criminal enforcement.
The operational shift towards centralised exchanges further exposes regulatory gaps. Exchanges operate globally but are supervised nationally. A breach in one jurisdiction can have financial consequences across many others. Even when stolen funds are identified quickly, freezing them depends on cooperation between regulators and law enforcement agencies that do not always share timelines or legal authority.
Laundering compounds the problem. Chainalysis and TRM Labs have shown that North Korean-linked funds are often moved rapidly across blockchains and informal trading networks before being converted into government-issued currency. Much of this activity occurs in regions where oversight is limited or unevenly applied. By the time sanctions authorities intervene, the assets may already have exited the regulated crypto sector.
Sanctions were built for a different financial architecture. Crypto has not made enforcement impossible, but it has made it slower and more dependent on international coordination. For governments operating under sanctions, those delays can be enough to move funds beyond reach.
This does not mean sanctions no longer work. It means they were designed for a financial system built around banks. Cryptocurrency has reduced the effectiveness of enforcement that depends on slow coordination and territorial jurisdiction. For a sanctioned state with limited alternatives, that shift has proved decisive.































